You may have seen the recent Harvard Business Review article in which Michael Porter and James Heppelmann describe How Smart Connected Products Are Transforming Competition. These smart connected products (a.k.a. the Internet of Things) are seen to be unleashing the third wave of IT-driven transformation and a new era of competition. Porter and Heppelmann say that the first two waves (the IT automation of the 1960s/70s followed by the Internet wave of 1980s/90s) radically reshaped competition and strategy, and delivered huge productivity gains and economic growth. However while these earlier waves transformed the value chain, products themselves were largely unaffected. The authors foresee the coming smart connected product wave will impact business models, industry structures and the very definition of industry itself … so I recommend downloading or reading the article online. Alternately Porter and Heppelmann presented The Rise of Smart Connected Devices keynote at last week’s LiveWorks 2015 conference in Boston which can be viewed online.
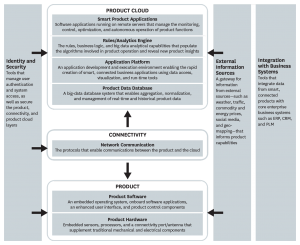
Porter and Heppelmann have developed a technology infrastructure model for smart connected products. This new technology stack is made up of multiple layers, including new product hardware, embedded software, connectivity, a product cloud consisting of software running on remote servers, a suite of security tools, a gateway for external information sources, and integration with enterprise business systems.
The authors also explore how companies can ride the wave to achieve sustainable competitive advantage (and as you would expect with Porter as co-author, the article examines this within the context of the five competitive forces) and the envisioned result of the third wave is …
Smart connected products ultimately can function with complete autonomy. Human operators merely monitor performance or watch over the fleet or the system, rather than over individual units.
… and I personally share this vision. However I do see two huge barriers.
Firstly Porter and Heppelmann’s technology template model is far too simple. The fact is that products at the edge will never pervasively be embedded with enough intelligence to undertake all the key monitoring, control and optimization functions required for an edge product to exhibit smart autonomy. Critical and major infrastructure edge products (vehicles, homes) will eventually have the extensive connectivity and rich real time processing capabilities built in – but this will never extend out to every “thing” being smart. Fortunately, the question is not simply whether to locate “smarts” in the edge product or in the cloud (as the authors would have us believe). Rather the question will be how to distribute the smarts throughout the layers that interconnect the edges, as well as in to the products and clouds at those edge. The template here is more akin with Cisco’s Fog model, where the cloud retains some central big data “think-tank” roles (analyzing data and making all the big decisions) with the array of the monitoring, analyzing and decision making tasks being delegated out and distributed to smart gateway products and network communications systems – as well as to edge products. So rather than Smart Connected Products we’ll have Smartly Connected Products. And the great challenge here will architecting open secure standards that can manage the distribution of the smarts – and then ensuring global adoption of these standards – so companies can craft new business operations that are robust, effective and interoperable.
Which segues into the second major hurdle and that is the issue of security in our new world of smartly connected things. With the current technology outlook, it is probable we will see pervasive interconnectivity between things with basic status reporting. However it unlikely most of these “things” will ever have the processing power and sophistication to detect an intrusion, let alone to protect themselves against violation. And as many of these smartly connected things will be empowered to autonomously impact human well-being, we’ll need to be architecting them with a level of care more akin to what we are used to in medical and drug domain (rather than what we see today with consumer appliances). I am confident an adequately sophisticated and appropriately enforced security solution model will evolve here, but the bulk of these security elements will be embedded in gateways* and distributed in layers of the communications networks, rather than in edge devices themselves.
* Gateway solutions like Opengear’s IM7200 Infrastructure Manager which just won a 2015 IoT Evolution Product of the Year Award from IoT Evolution magazine.